Multiple Reflected Cross-Site Scripting Vulnerabilities in Three WordPress Plugins Patched
The Wordfence Threat Intelligence Team recently disclosed several Reflected Cross-Site Scripting vulnerabilities that we discovered in three different plugins – Watu Quiz (installed on 5,000 sites), GN-Publisher (installed on 40,000 sites), and Japanized For WooCommerce (installed on 10,000 sites). As with all Reflected Cross-Site Scripting vulnerabilities, these could be leveraged for a complete site takeover as long as an unauthenticated attacker could successfully trick a site administrator into performing an action, such as clicking on a link or visiting a website under the attacker’s control.
All Wordfence customers, including Wordfence Premium, Wordfence Care, and Wordfence Response customers as well as those still using the free version of our plugin, are protected against any exploits targeting these vulnerabilities by the Wordfence firewall’s built-in Cross-Site Scripting protection.
Vulnerability Summaries
Affected Plugin: Watu Quiz
Plugin Slug: watu
Affected Versions: <= 3.3.9
CVE ID: CVE-2023-0968
CVSS Score: 6.1 (Medium)
CVSS Vector: CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N
Researcher/s: Marco Wotschka
Fully Patched Version: 3.3.9.1
Affected Plugin: GN Publisher: Google News Compatible RSS Feeds
Plugin Slug: gn-publisher
Affected Versions: <= 1.5.5
CVE ID: CVE-2023-1080
CVSS Score: 6.1 (Medium)
CVSS Vector: CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N
Researcher/s: Marco Wotschka
Fully Patched Version: 1.5.6
Affected Plugin: Japanized For WooCommerce
Plugin Slug: woocommerce-for-japan
Affected Versions: <= 2.5.4
CVE ID: CVE-2023-0942
CVSS Score: 6.1 (Medium)
CVSS Vector: CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N
Researcher/s: Marco Wotschka
Fully Patched Version: 2.5.5
Vulnerability Details
Watu Quiz is a plugin that offers site owners the ability to create exams, quizzes and surveys. It allows administrators to review quiz submissions and filter search results by username, email, date taken and quiz score. Unfortunately, the search terms – provided as URL parameters – were not properly sanitized before being echoed on the search form.

Visiting a URL containing a malicious payload sufficed to trigger the execution of malicious JavaScript code in the context of the visiting user’s session. Since the exploitable page was an administrative page, this code could be used to create new administrator users or to perform other similarly severe actions potentially resulting in site takeover.
A vulnerable line of code in the plugin used the user-provided parameter and output it directly:
<input name="dn" type="text" value="<?php echo @$_GET['dn']?>" />
The dn parameter can be used to close out the value attribute, add an onmouseover event (or an onfocus event combined with the autofocus attribute) and execute JavaScript in the context of the victim’s browser.
/wp-admin/admin.php?page=watu_takings&exam_id=1&dn="%2Fonmouseover%3Dalert(123)%2F%2F
Versions up to 3.3.9 of this plugin are vulnerable. The issue is fixed in version 3.3.9.1 as of March 3, 2023.
GN Publisher is a plugin that makes RSS feeds which comply with Google News RSS feed technical requirements – necessary for inclusion in the Google News Publisher Center. The plugin addresses some common RSS compatibility issues publishers typically experience.
On its main configuration page It offers a tabbed form where administrators can change plugin-specific settings. However, the plugin does not properly escape the tab name before outputting it.
The software features a button in the top right corner that offers an upgrade to the PRO version. The code for the button in the vulnerable version is shown below (slightly reformatted for legibility):
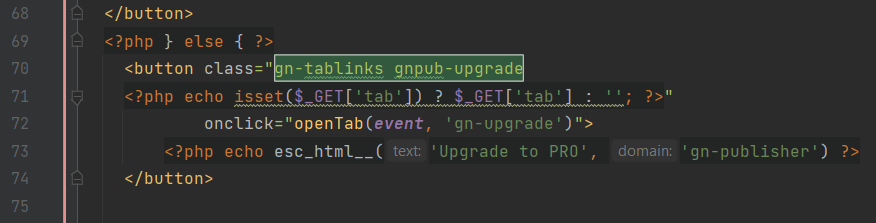
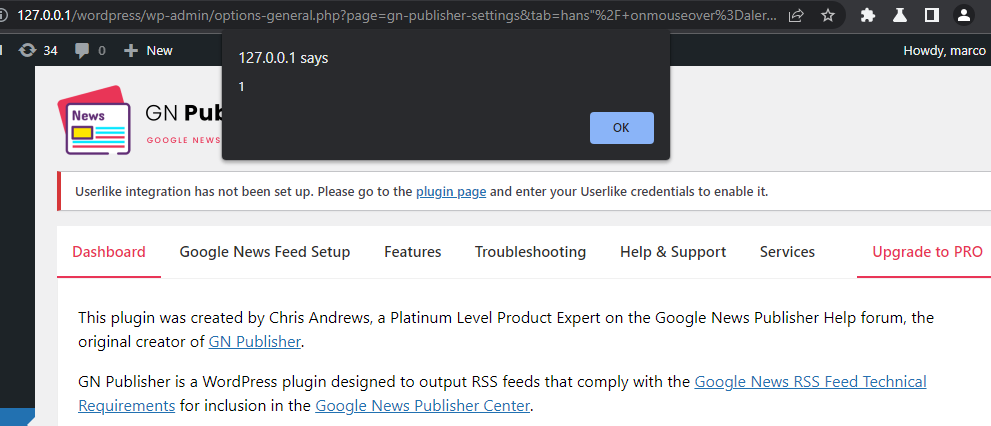
As can be seen, the button element contains a php echo statement that outputs the tab parameter as a button class attribute. An unauthenticated attacker can take advantage of this and inject attribute-based JavaScript that executes on an event of the attacker’s choosing such as onmouseover, or onfocus in combination with autofocus, assuming they can also successfully trick a site administrator into performing an action.
/wp-admin/options-general.php?page=gn-publisher-settings&tab=hans%22%2F+onmouseover%3Dalert%281%29%3B%2F%2F
Versions up to, and including, 1.5.5 are vulnerable. Version 1.5.6 addressed this issue and was released on February 24, 2023.
The plugin Japanized for WooCommerce adds additional features to WooCommerce that make it more user-friendly for a Japanese audience, such as honorific titles and custom payment options geared towards the Japanese market. Similarly to the other two plugins discussed above, Japanized for WooCommerce outputs unsanitized user input provided via URL parameter.
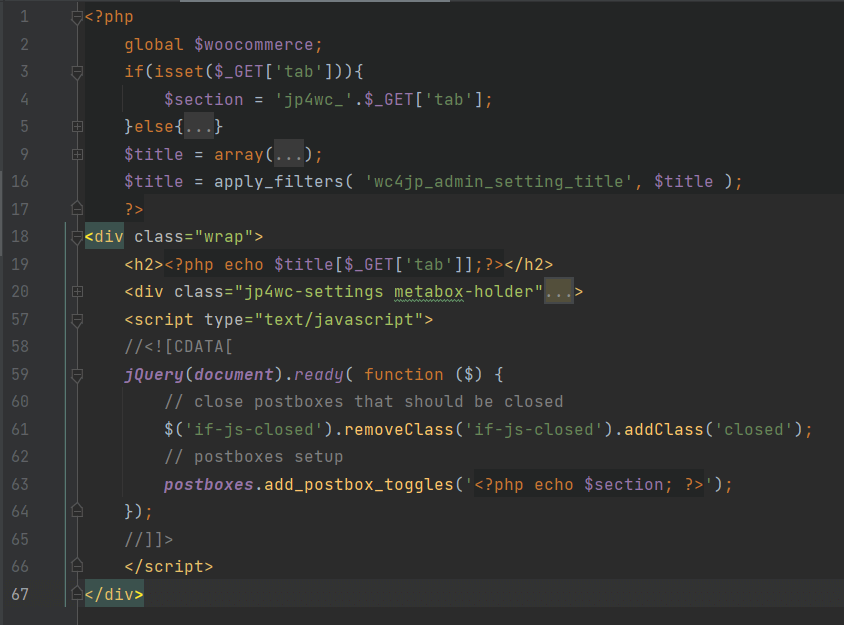
As long as a tab parameter is provided, it will be output as part of the provided JavaScript that follows. A malicious piece of code can be used to close the script tag, open a new one, and include code to be executed on behalf of the visiting user.
/wp-admin/admin.php?page=wc4jp-options&tab=hans%27%3C%2Fscript%3E%3Cscript%3Ealert%281%29%3C%2Fscript%3E
Just like the other two vulnerabilities discussed above, this vulnerability can be exploited by unauthenticated attackers as long as an administrator of a vulnerable site can be tricked into performing an action such as clicking on a link leading them to the vulnerable form.
This issue is patched as of version 2.5.6, which was released on February 28, 2023.
As a final reminder, as is typical for Reflected Cross-Site Scripting vulnerabilities, these attacks can be carried out by unauthenticated users. However, the interaction of a site user is a requirement. Furthermore, the malicious injection does not persist as it is not stored in the database.
Conclusion
In today’s post, we detailed flaws in three plugins that made it possible for attackers to inject malicious JavaScript into a vulnerable site. While the exploitation of these vulnerabilities requires some degree of social engineering, they all could be used for site takeover.
All Wordfence users, including those running Wordfence Premium, Wordfence Care, and Wordfence Response, as well as sites still running the free version of Wordfence, are fully protected against this vulnerability.
If you believe your site has been compromised as a result of these vulnerabilities or any other vulnerability, we offer Incident Response services via Wordfence Care. If you need your site cleaned immediately, Wordfence Response offers the same service with 24/7/365 availability and a 1-hour response time. Both these products include hands-on support in case you need further assistance.
If you have any friends or colleagues who are using one of these plugins, please share this announcement with them and encourage them to update to the latest version as soon as possible.
If you are a security researcher, you can responsibly disclose your finds to us and obtain a CVE ID and get your name on the Wordfence Intelligence leaderboard.
Comments